Install Tinc and VPN Setup on Debian & Ubuntu
Tinc is a Virtual Private Network (VPN) daemon that uses tunnelling and encryption to create a secure private network between hosts on the Internet.
A few of the features that Tinc has that makes it useful include encryption, optional compression, automatic mesh routing (VPN traffic is routed directly between the communicating servers, if possible), and easy expansion. These features differentiate Tinc from other VPN solutions such as OpenVPN, and make it a good solution for creating a VPN out of many small networks that are geographically distributed. Tinc is supported on many operating systems, including Linux, Windows, and Mac OS X.
Tinc Setup
Tinc is a self-routing, mesh networking protocol, used for compressed, encrypted, virtual private networks.
Prerequisites
To complete this tutorial, you will require root access on at least three Ubuntu 14.04 servers. Instructions to set up root access can be found here (steps 3 and 4): Initial Server Setup with Ubuntu 14.04.
If you are planning on using this in your own environment, you will have to plan out how your servers need to access each other, and adapt the examples presented in this tutorial to your own needs. If you are adapting this to your own setup, be sure to substitute the highlighted values in the examples with your own values.

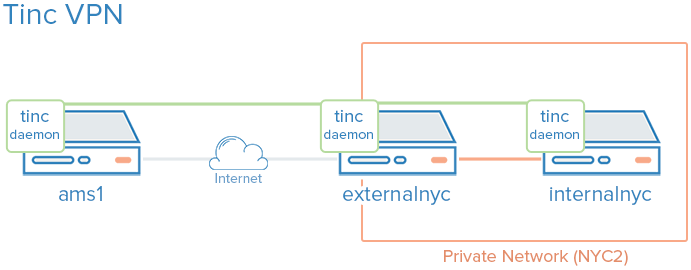
If you would like to follow this tutorial exactly, create two VPSs in the same datacenter, with private networking, and create another VPS in a separate datacenter. We will create two VPSs in the NYC2 datacenter and one in AMS2 datacenter with the following names:
- externalnyc: All of the VPN nodes will connect to this server, and the connection must be maintained for proper VPN functionality. Additional servers can be configured in a similarly to this one to provide redundancy, if desired.
- internalnyc: Connects to externalnyc VPN node using its private network interface
- ams1: Connects to externalnyc VPN node over the public Internet
Tinc Configuration
Tinc uses a “netname” to distinguish one Tinc VPN from another (in case of multiple VPNs), and it is recommended to use a netname even if you are only planning on configuring one VPN. We will call our VPN “netname” for simplicity.

Macbook, iPad and iPhone
The ping should work fine, and you should see some debug output in the other windows about the connection on the VPN. This indicates that ams1 is able to communicate over the VPN through externalnyc to internalnyc. This indicates that ams1 is able to communicate over the VPN through externalnyc to internalnyc.
Continue reading this guide at Digital Ocean. This article has been used as an example of an Ecko WordPress theme. This work is licensed under a Creative Commons Attribution-NonCommercial-ShareAlike 4.0 International License.


Comments which are made by the author are marked with the ‘Author’ tag, such as this one. Replies to posts are indented.
Replies are indented to the right of the original post, such as this one.